We all know to watch for suspicious emails. But phishing emails are becoming increasingly more sophisticated, tricking even the savviest among us. The costs to consumers, businesses and institutions keep adding up: According to the FBI, online theft, fraud and exploitation totaled $2.7 billion in financial losses in 2018.
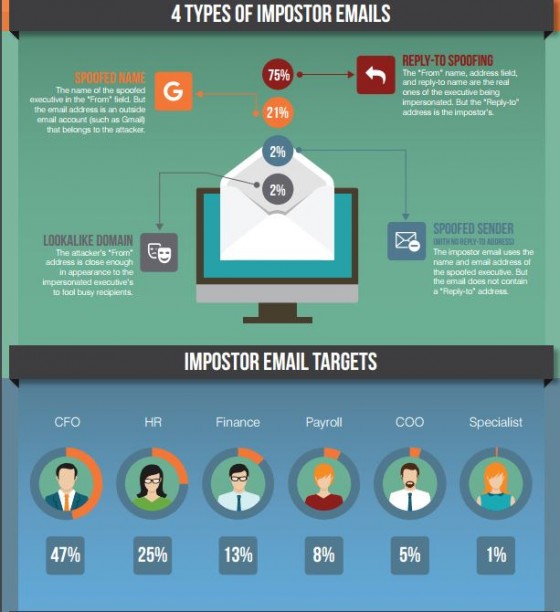
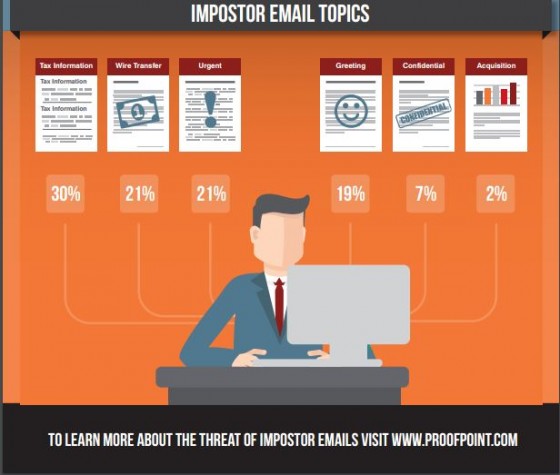
The most expensive complaints involve business email compromise (BEC), a tool that cybercriminals use to launch many types of cybercrimes, from misdirected payment and inventory fraud to ransomware attacks.
More than a third of businesses (37%) surveyed nationally for HSB by Zogby Analytics received an email from someone pretending to be a senior manager or vendor requesting payments. The businesses reported that almost half of employees receiving those emails (47%) responded by transferring company funds, resulting in tens of thousands of dollars in losses. For some types of businesses and government entities, the payment frauds can reach hundreds of thousands to millions of dollars.
Three Tips to Help Employees Avoid Cyber Fraud
What can a business or institution do to help prevent employees from falling for email phishing schemes? Here are three tips to avoid falling for the latest tricks:
- Check the Source
Before you open an email, take a moment to consider the source of the email and whether that person is likely to send you an attachment or link. Check the email address, screen name or phone number associated with the message.
Hackers often mimic an email address that you would trust with one letter or number off from the original name or domain.
The address may even look exactly like a trusted contact but when you mouse-over the name, you can see that the address is different. A hacked email account can also be used to send malicious content, so be sure to evaluate the content of the message.
- Check the Content
Before you click on a link or download an attachment, take a good look. Many times, if you copy the link or name of the attachment into a search engine, you can find out whether cybercriminals are actively using the content to spread malicious content, like a virus or ransomware.
Ask yourself whether this is the type of content you usually receive from the sender. Are you expecting an attachment? Even if you are expecting an attachment, does it appear, from the name and type of file, that it is legitimate? Is the attachment or link the only content of the email?
If you have doubts, delete the message or call the sender at a number you have verified as theirs.
Also, hackers often make an urgent request to trick victims into clicking on malicious links or files. Any urgent request sent via email should be verified in-person.
- What if I Clicked on the Wrong Thing?
Everyone makes mistakes. You would not be the first person to click on a bad link or download a bad file. But even if nothing happens immediately, there is no guarantee that the threat is gone.
Malware can lay dormant for weeks, months, or even years before activation. It may also be transmitting information in the background without your knowledge.
So, act as soon as you realize you clicked on a bad link or file. Alert your information technology security department right away. If you are a smaller operation, run a virus scan and keep an eye on your financial information.