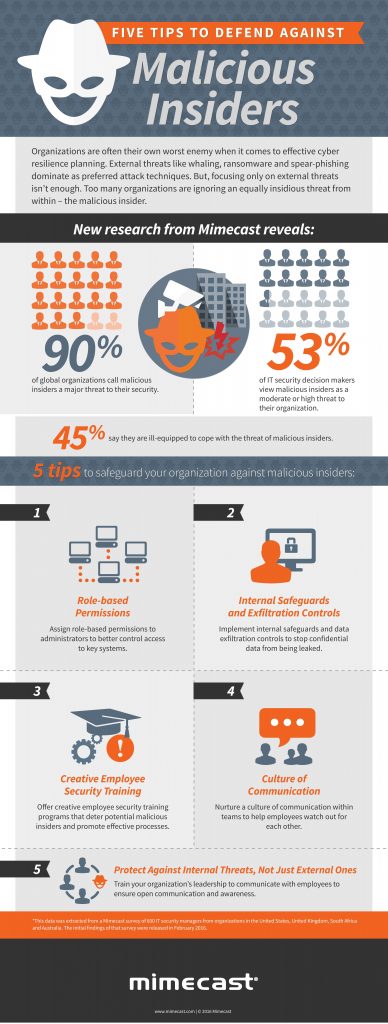
Months into the pandemic, organizations have recovered from the initial emergency of trying to ensure that their employees could safely work from home. They now realize that this remote reality will be extended—and they need to determine if they have the right cybersecurity protections in place. Most importantly, they need to stop insider threats, which account for more than 30% of all data breaches.
A long-term commitment to remote work requires a commitment to stopping data loss due to compromised, negligent, or malicious insiders. According to the Ponemon Institute, before the pandemic, the average annual global cost of insider threats rose by 31% in two years to $11.45 million, and the frequency of incidents spiked by 47% in the same period. Security teams are in a constant battle to stop cybercriminals from stealing employee credentials, prevent malicious employee action, and correct accidental user behaviors—all of which can result in unintended data loss. Three ways to reduce insider threat risk are:
1. Conduct a Comprehensive Insider Threat Risk Assessment
Each organization has a unique set of risks from insider threats. Be sure to complete a comprehensive risk assessment to identify your most important data and systems, who can access them, and the security controls you have in place to protect your organization. It is important to remember that data loss potential increases every time new information is created and stored. An organization’s most valuable assets (its people, including employees, contractors and partners) can also become its greatest vulnerability without sufficient data controls in place.
After assessing your environment, focus on identifying key risks and weaknesses to address. Successful elements include building a dedicated insider threat function to protect sensitive data, investing in training, and providing real-time policy reminders for users. Work with your HR team to educate and empower employees in subjects like secure data handling, security awareness, and vigilance. Following these steps will address and mitigate insider threats while establishing consistent, repeatable processes that are fair to all employees.
2. Place People at the Center
From a risk standpoint, organizations must place people at the center of their overall cybersecurity strategy—especially as the workforce becomes more distributed. According to Proofpoint, more than 99% of cyberattacks require human interaction to be successful. Chances of a successful attack only increase when employees are remote. Ultimately, data does not just get up and walk away—it requires someone to perform an action. So a people-centric security approach is necessary to mitigate critical risks across email, the cloud, social media and the web.
First, significantly limit access to non-essential data. Second, limit how long specific users can access the information they need to complete a task. For example, not everyone needs access to customer records. Be sure your security technology can differentiate between malicious acts, accidental behavior, and cybercriminal attacks using compromised employee accounts. This intelligence helps organizations respond according to the incident and provides context around the activities that took place.
Finally, detecting and preventing insider threats is a team sport. It is important to ensure the right stakeholders from each department are involved in your security program. This should include operations, human resources, IT, legal, and of course security.
3. Insider Threat Technology at Work
Organizations need to take a holistic approach to combating insider threats, especially during the pandemic. When assessing insider threat technology, be sure to first consider the performance impact of any solution and its associated scalability, ease of management, deployment, stability and flexibility. Select a solution that provides visibility into user behavior while complementing the tools your organization already uses.
A dedicated insider threat solution reduces threats by helping organizations identify user risk, prevent data loss, and accelerate incident response. This approach also distinguishes malicious acts from simply careless or negligent behavior.
A more comprehensive cybersecurity program, while also putting training in place, can address negligent behavior before it becomes a security concern.
In 2020, everything about how and where we work changed.
Unfortunately, both external and insider data breaches are accelerating. Organizations are losing more data due to compromised, negligent, or malicious insiders, so it is time to place people at the center of your cybersecurity strategy. Today’s COVID-19 reality weighs heavily on security teams.
An effective combination of people, process, and technology can help remediate one of the most critical risk factors facing organizations around the world today.