Nearly two years ago, an infamous incident occurred where stolen pictures of celebrities flooded the internet. Originally, it was thought that this was due to an iCloud vulnerability that allowed a brute force attack. But it now turns out it was because of a simple social engineering phishing hack.
Phishing usually involves sending mass emails that masquerade as legitimate communications, coming from a trustworthy source like a big bank or credit card company. The phisher seeks to trick the recipient into clicking on a link or opening an attachment that downloads malware onto the victim’s computer. The malware can then be used for criminal activity including theft of sensitive data or money. While phishers may send thousands of emails, all they need are a few or even one individual to fall for their trick to get into the IT system. It’s easy to forget that security threats aren’t always the work of sophisticated technology geniuses with malevolent intent. As in the case of the celebrity photos, the method was relatively simple. However, it still caused reputational damage.
Cyber attacks don’t appear out of nowhere.
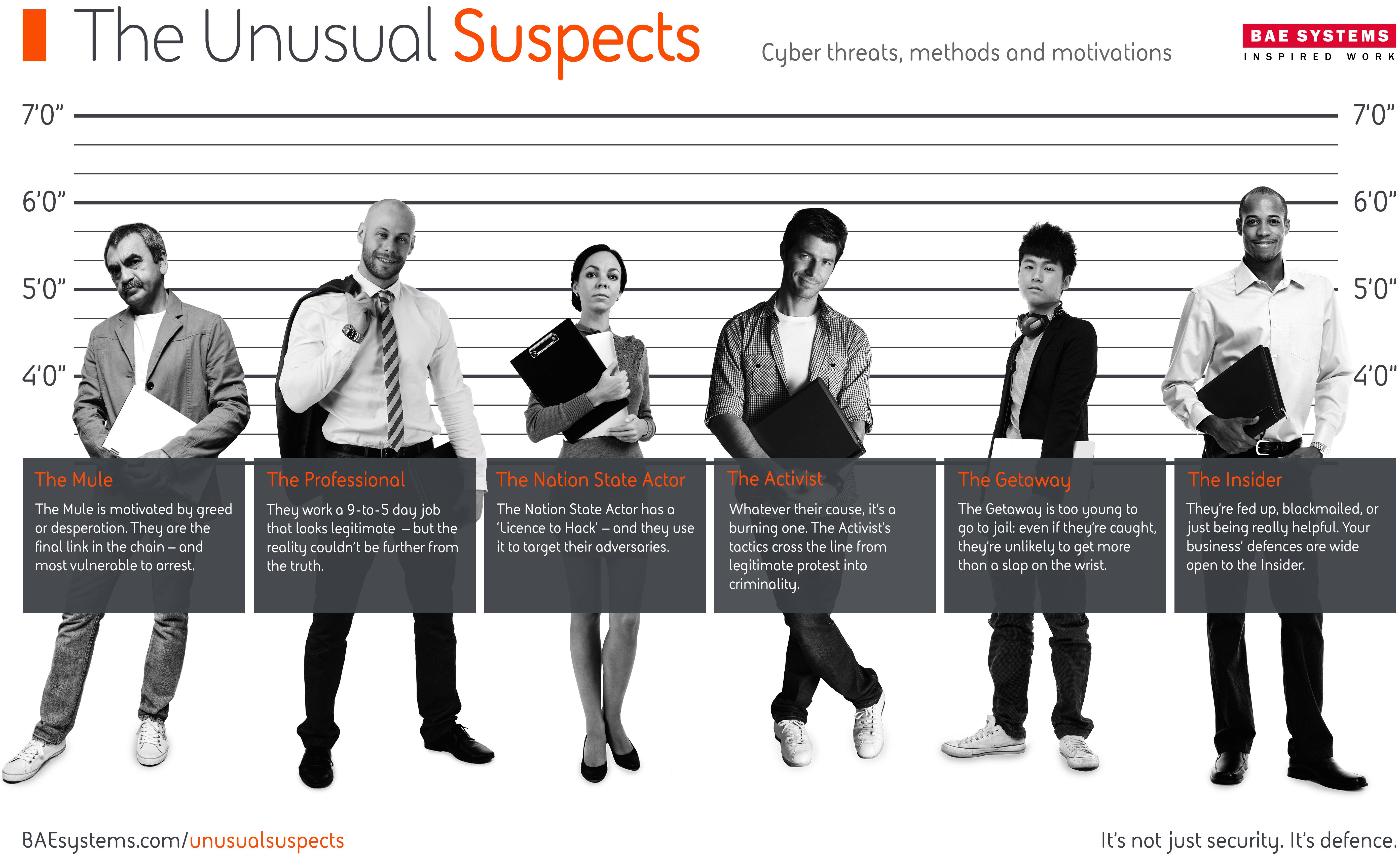
At the beginning and right through development and attack, humans are involved. Recently, we profiled half a dozen types of attackers. We call them the “Unusual Suspects.” An attack might start with the Professional working in the digital shadows seeking to make the most money possible from the damage they cause. Then you’ve got the Mules and Getaways who are on the front line, and will be the first to get caught when the law comes knocking. There are also Activists and Nation State Actors who are looking to change the world or steal information on behalf of their country’s government. And then there’s the Insider leaking sensitive information accidentally or on purpose with malicious intent.
These are all just some of personas BAE Systems recently identified as key threats to businesses and without them, cybercrime can’t exist.
Wising up to phishing attacks
In the IT space, one of the most common ways cyber criminals target employees of a company is through phishing. In the aforementioned celebrity photos case, court documents said Ryan Collins, 36, of Pennsylvania, hacked more than 100 people. According to reports in the press he used email names like ‘e-mail.protection318@icloud.com’ and asked for password details.
With these credentials, the hacker was able to go through email accounts looking for photos and videos, managing to get into around 50 iCloud accounts and 72 Gmail accounts mostly belonging to celebrities. It’s quite easy to imagine the damage hackers could cause if they got hold of corporate emails – think of the damage the 2014 Sony hack inflicted.
You can’t patch a human
Employees will always be a weak spot, and clever social engineering is leading to more examples of how this weakness can be exploited. The effects can be devastating. For example: a company that collects credit card data from its customers is at risk of a major data breach from a single employee clicking on an email leading to a website laced with malware. The financial and/or reputational damage and the related fines or compensation claims that result could be significant.
At its core, combating social engineering is a human problem that requires human solutions. In certain cases victims may violate policies, but it may often be the case that the rules or training were not clear enough for the employee to know they were doing something that could have serious consequences. And because humans are behind social engineering attacks, they are capable of evolving, matching the way the business world is using technology.
To mitigate against social engineering attacks, there needs to be security awareness and culture from top to bottom. This might mean ongoing training for employees to understand the threats, as well as the right policies and procedures in place. This helps employees understand the risk from social engineering and what role they have in preventing it. Remember, this all has to be done in tandem with putting the right technology in place.
Defeating the Unusual Suspects
Defending against cyber threats is all well and good, but what about catching these Unusual Suspects? This is difficult, because they use sophisticated tactics to escape detection–they are located all over the world, and use secure software to escape detection and remain anonymous, often routing communications through multiple countries to avoid being caught.
Fortunately this is a case where human fallibility is a good thing–criminals will make mistakes and leave digital finger prints that sophisticated analytics and forensic analysis can pick up. Finally don’t underestimate the power of human ingenuity–thanks to the efforts of security professionals, we’re finally getting to a point where the investigation of online crime is being slowly demystified and defenses put in place to mitigate the threat.